In the digital age, cybersecurity asset management is more critical than ever. Businesses must keep track of their assets to protect sensitive data and ensure operational efficiency. This guide will explore the principles of cybersecurity asset management, its importance, and how CloudBlast can enhance your asset management strategy.
What is Cybersecurity Asset Management?
Cybersecurity asset management involves identifying, tracking, and managing all physical and digital assets within an organization. These assets can include hardware, software, data, and network resources. Proper management is essential for maintaining security, compliance, and efficiency.
Importance of Asset Management in Cybersecurity
- Enhanced Security: By having a comprehensive inventory of assets, organizations can better protect them from cyber threats. Knowing what assets exist and where they are located helps in identifying vulnerabilities and implementing targeted security measures.
- Regulatory Compliance: Many industries have strict regulations regarding data protection and asset management. Effective asset management ensures that organizations meet these regulatory requirements, avoiding potential fines and penalties.
- Operational Efficiency: With a clear overview of assets, businesses can optimize their use, reduce redundancies, and ensure that resources are allocated efficiently.
- Risk Management: Identifying and managing assets allows organizations to assess risks accurately and prioritize security measures accordingly.
Key Components of Cybersecurity Asset Management
- Asset Discovery: The first step is identifying all assets within the organization. This includes hardware, software, and network components.
- Asset Tracking: Once identified, assets must be tracked to monitor their status, location, and usage. This helps in maintaining up-to-date records.
- Vulnerability Management: Regularly scanning assets for vulnerabilities ensures that potential threats are identified and mitigated promptly.
- Lifecycle Management: Managing the full lifecycle of assets—from acquisition to disposal—ensures that security measures are maintained throughout.
How CloudBlast Supports Cybersecurity Asset Management
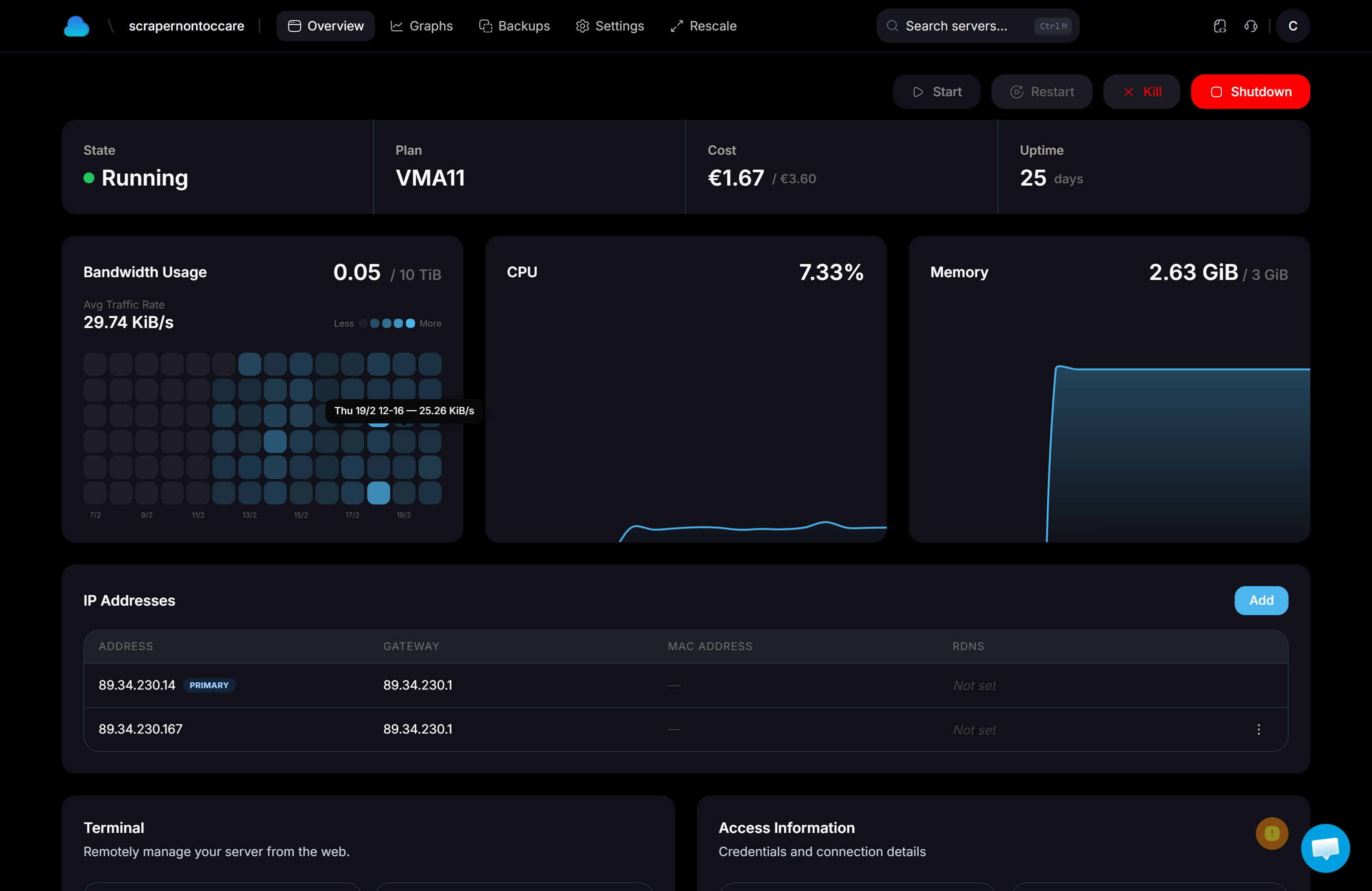
CloudBlast provides comprehensive solutions for cybersecurity asset management. By utilizing CloudBlast's tools, organizations can automate asset discovery, streamline tracking processes, and enhance their overall security posture.
- Automated Asset Discovery: CloudBlast’s platform automatically identifies new and existing assets, ensuring that no component is overlooked.
- Real-Time Monitoring: Gain real-time insights into asset status and vulnerabilities, allowing for swift responses to potential threats.
- Compliance Reporting: Simplify compliance with automated reporting features that help track and document asset management efforts.
Conclusion
Effective cybersecurity asset management is crucial for protecting organizational assets and ensuring compliance with industry regulations. By partnering with CloudBlast, businesses can enhance their asset management strategies, improving security and operational efficiency. Stay ahead of cyber threats and manage your assets with confidence using CloudBlast’s advanced asset management solutions. Embrace a proactive approach and safeguard your organization’s digital future today.