In today's digital landscape, securing your server is paramount to safeguarding sensitive data and maintaining the integrity of your online presence. This guide delves into the essential aspects of server security, highlighting common threats and offering practical strategies to fortify your defenses. Additionally, we'll introduce CloudBlast, a robust solution for enhancing your server's security posture.
Understanding Server Security Threats
Server security involves protecting your systems from unauthorized access and malicious attacks. Common threats include:
- Brute Force Attacks: These involve attackers using automated tools to guess login credentials by trying numerous combinations. Even with SSH key authentication, brute force attacks can be effective if not properly mitigated
- Distributed Denial of Service (DDoS) Attacks: In a DDoS attack, the attacker overwhelms the server with a flood of HTTP requests, causing service disruptions. This type of attack exploits poor server configurations and can severely impact server availability
- SQL Injection and Other Code Injections: These attacks exploit vulnerabilities in your server's software to execute malicious code, potentially leading to data breaches and unauthorized access.
Best Practices for Server Security
To protect your server from these threats, consider implementing the following best practices:
- Regular Updates and Patching: Keep your operating system and all software up-to-date with the latest security patches. This minimizes vulnerabilities that attackers can exploit
- Strong Authentication Mechanisms: Use strong, unique passwords and consider implementing two-factor authentication to add an extra layer of security.
- Firewall Configuration: Properly configure firewalls to restrict access to only necessary services and ports. This helps prevent unauthorized access and reduces the attack surface.
- Secure Data Transmission: Use SSL/TLS certificates to encrypt data in transit, ensuring that sensitive information is protected from interception
- Comprehensive Logging and Monitoring: Implement robust logging systems to detect and respond to suspicious activities in real-time. This is crucial for identifying potential security breaches early.
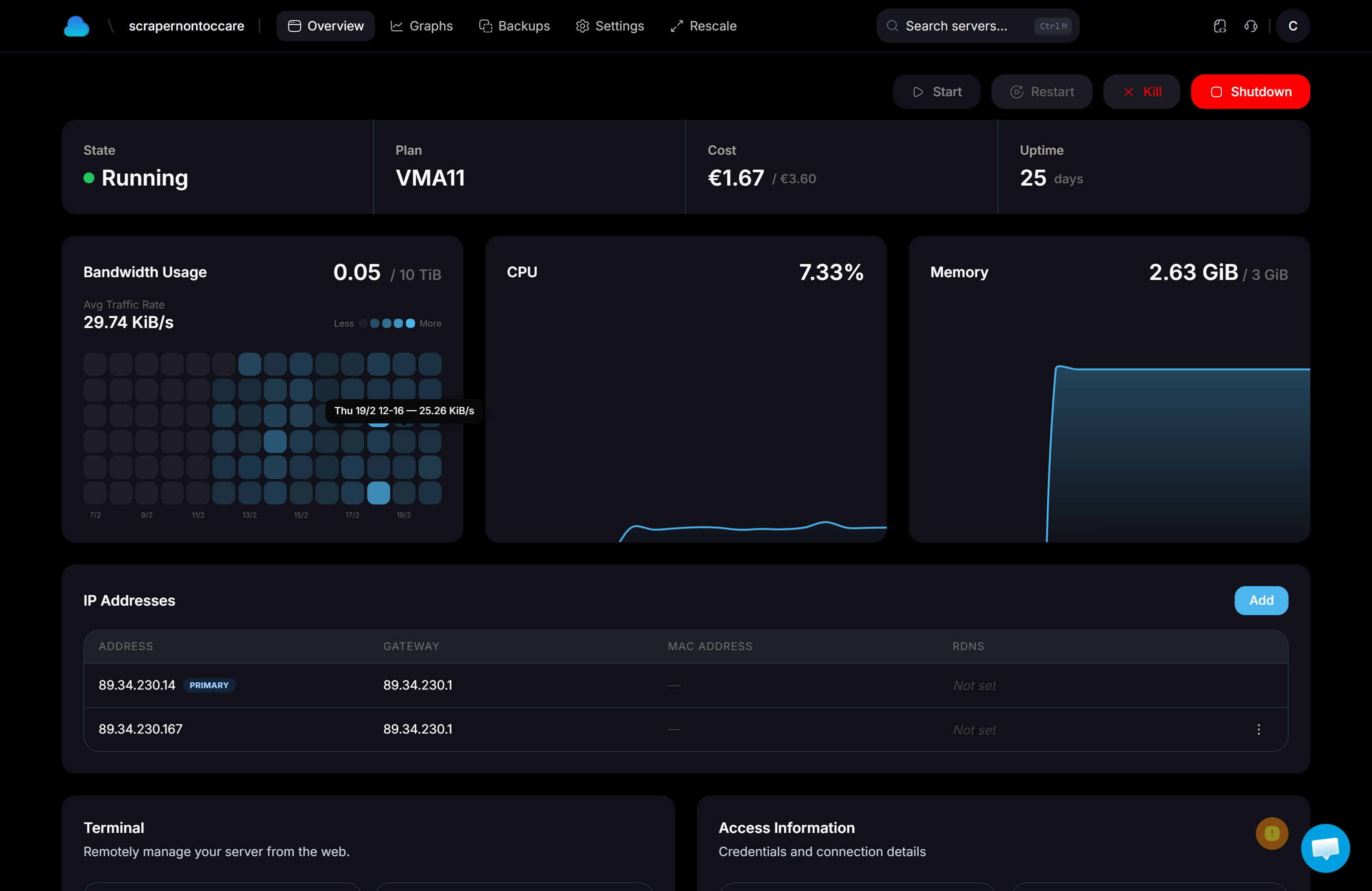
Introducing CloudBlast
For those seeking an advanced solution to enhance server security, CloudBlast offers a comprehensive suite of tools designed to protect against a wide range of cyber threats. With features like automated threat detection, real-time monitoring, and seamless integration with existing infrastructure, CloudBlast empowers businesses to maintain a secure and resilient server environment.
Conclusion
Securing your server is an ongoing process that requires vigilance and the implementation of best practices. By understanding common threats and leveraging solutions like CloudBlast, you can significantly enhance your server's security and protect your valuable data from malicious actors. Stay proactive and informed to ensure your server remains a robust and secure component of your digital operations.